Will your endpoint protection actually block ransomware and cryptomining infections
Bad actors are constantly coming out with new versions of ransomware strains to evade detection. Is your endpoint protection software effective in blocking ransomware when employees fall for social engineering attacks?
KnowBe4’s Ransomware Simulator gives you a quick look at the effectiveness of your existing endpoint protection. Ransomware Simulator will simulate 22 ransomware infection scenarios and 1 cryptomining infection scenario to show you if a workstation is vulnerable.
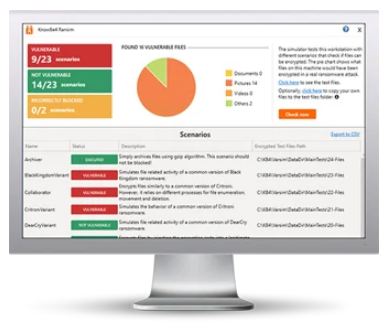
Here's how RanSim works
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 23 types of infection scenarios
- Just download the installer and run it
- Results in a few minutes!
This is complimentary and will take you 5 minutes max. Ransomware Simulator may give you some insights about your endpoint security you never expected!
NOTE: Ransomware Simulator was created for Windows-based workstations running Windows 7+. Ransomware Simulator does notalter any existing files on disk. As part of the simulation Ransomware Simulator does enumerate all files on the local disk(s). For the purposes of encryption, simulated data files are downloaded from the Internet.
Ransomware Defined
Ransomware is defined as vicious malware that locks users out of their devices or blocks access to files until a sum of money or ransom is paid. Ransomware attacks cause downtime, data loss, possible intellectual property theft, and in certain industries an attack is considered a data breach.
Ransomware Hostage Rescue Manual
What You Need to Know to Prepare and Recover from a Ransomware Attack
This manual, from our trusted partner KnowBe4, is packed with actionable info that you need to prevent infections, and what to do when you are hit with ransomware.
You will also receive a Ransomware Attack Response Checklist and Ransomware Prevention Checklist.